Connecting state and local government leaders
Resilient voting systems and fail-safes are needed by the midterm elections, when backdoor access to state tabulators is expected to be for sale on the “dark web.”
WASHINGTON — The international cyberattack that infected computers with malware in at least 150 countries late last week, including 48 National Health Service trusts in the United Kingdom, exploited an old vulnerability first used by the National Security Agency. NHS was particularly hard hit because most of its hospitals use Windows XP, the same software most U.S. voting systems run on.
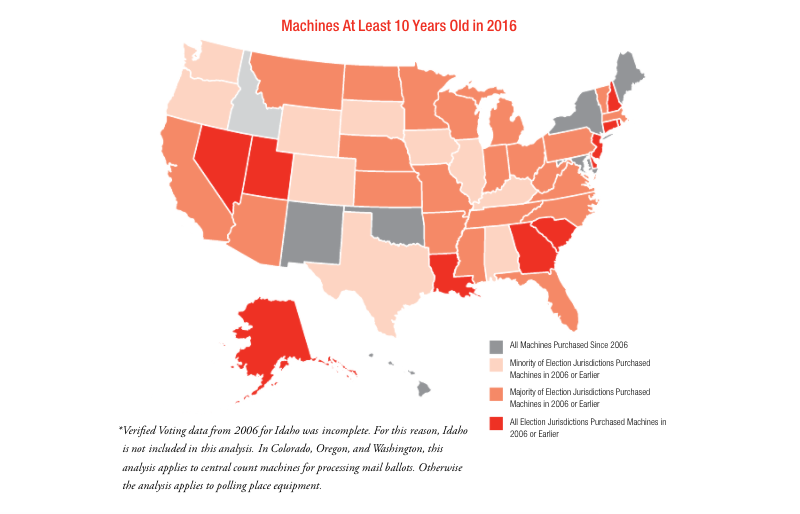
A total of 42 U.S. states still rely on voting systems more than a decade old—close to the end of their projected lifespan.
Among counties with such systems, a disproportionate number fail to back them up with a paper ballot and mandated, risk-limiting audits of the final vote.
“Come 2020, we’re going to be sitting ducks,” said J. Alex Halderman, a computer science professor at the University of Michigan, at a congressional briefing on Monday.
The decision of which of the 52 available voting technologies to use generally falls to counties, and not a single one tested by security experts—direct-recording electronic or optical scan—has withstood the spread of vote-stealing malware, which interferes with the records as they’re created to change the result.
Simply diversifying and decentralizing voting tech and disconnecting machines from the internet isn’t enough to stop even a middling hacker, Halderman said.
In a close race, diversity is a weakness because attackers will likely have several key jurisdictions to choose from, using pre-election polling as a guide, when affecting the outcome. And even if voting machines are disconnected from the internet, the election management system that programmed the ballot design onto their memory cards prior to the vote wasn’t—meaning the hack could have occurred ahead of time.
Memory cards still offer a faster, cheaper tally, but thoroughly auditing a statistically significant sample of backup paper records is the only way to ensure electronic results.
Vote-stealing malware can be coded to alter only 10 percent of the vote so as to stay below the radar. That said, there is no proof any previous U.S. election has been compromised this way.
“Last election wasn’t hacked,” said retired Army Lt. Col. Tony Shaffer, a senior fellow at the London Center for Policy Research. “Elements of different cyber issues were presented.”
Who would want to hack a U.S. election? China for starters, said James Scott, senior fellow at the Institute for Critical Infrastructure Technology. Also, Iranians actively sought a toolkit on the “dark web,” during the last presidential election, to hack Pennsylvania’s central tabulator, Scott said.
The biggest threat remains Russia, which revealed in 1989, when the Soviet archives were briefly opened, that its disinformation officers outnumbered military personnel.
“The Russians are good at cyber,” said James Woolsey, former CIA director and chair of the Foundation for Defense of Democracies. “They have always been good mathematicians.”
Cyber helps Russia magnify the effects of their disinformation campaign, and they gladly share their knowledge with other enemies of the U.S., such as when they gave North Korea the details on an extremely fast torpedo. Many of the U.S.’s own cyber techniques from the 1990s and 2000s have been subverted and expanded, Shaffer said.
Current tactics to co-opt the vote involve spear phishing email and social links that, when clicked, initiate the drive-by download of compiled tools: remote-access Trojan viruses; virus droppers; keyloggers; screen grabbers; camera and mic capture tools; network mappers; code injectors; innovative malware like Russia’s HAMMERTOSS, which uses Twitter to relay commands and extract data; tabulation manipulators that weigh the vote to appear legitimate; and geo-targeting only activated in swing states or regions.
Should an attacker steal network credentials, they can lay the groundwork for future attacks by securing remote access and then selling, on the dark web, that backdoor “access as a service.” By the 2018 midterm elections, access to state tabulators will be purchasable, Scott said.
Local elections are naturally the most vulnerable, with state and local employees notorious for checking their social media accounts from the office. All it takes is clicking the wrong bit.ly link.
“Twitter will continue to be the main distribution vector, and the most successful vector, for all of this stuff,” Scott said.
Waiting until the next presidential to address vulnerabilities that have been public for years is a mistake, Woolsey said.
But currently all state bills seeking resilient systems that can withstand cyberattacks, paper ballots and mandatory audits have been sponsored and cosponsored solely by Democrats, said Lawrence Norden, deputy director of the Brennan Center for Justice at the New York University School of Law.
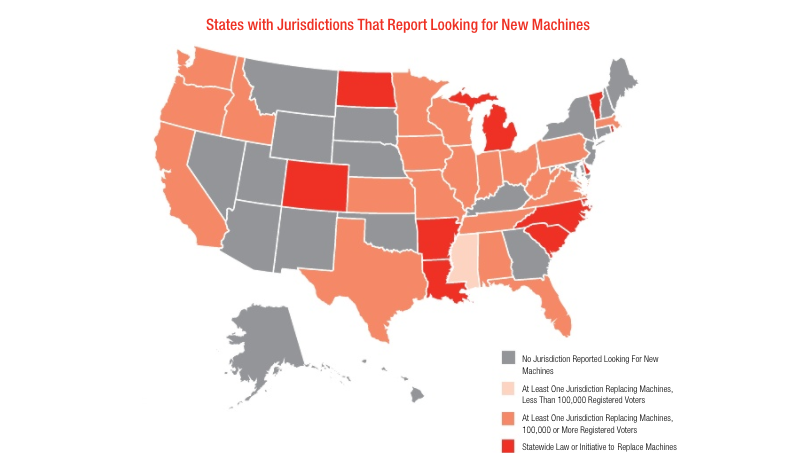
Part of the problem is state and county officials are defensive of their power to run elections as they see fit. Yet those elections are “chronically underfunded,” Norden said, which provides an opening for the federal government to offer innovation grants or some sort of match to replace machines and invest in a thorough audit.
Most states want new voting machines, but 80 percent of the states looking informed the Brennan Center they were unsure of where the money would come from, according to “America’s Voting Machines at Risk.”
Shaffer said he was surprised the Freedom Caucus, who he works with, hadn’t come to the table on the issue. Partisanship being at an all-time high, Woolsey suggested seeking financial assistance from wealthy benefactors or foundations might be a more feasible funding approach.
“It absolutely should be a bipartisan effort because we’re...talking about systems that are essential to the functioning of our democracy,” Halderman said.
Constituents want security by design in new tech and improved cyber hygiene, Scott said. The Cyber Shield Act, which ICIT supports, is a start.
Cyber paranoia surrounding the 2016 election continues to be felt, as the reality of an impending threat mounts. Even the perception of an election hack is dangerous at this point.
“This is a chess game. We have to play this as a chess game,” Shaffer said. “A well-funded, well-versed adversary, simply by thinking things through, could undermine the process without using any new technology."
Dave Nyczepir is a News Editor for Government Executive’s Route Fifty and is based in Washington, D.C.

NEXT STORY: VA seeks indoor navigation app
![A voter feeds a bal, ... ]](https://cdn.route-fifty.com/media/img/cd/2017/05/16/vote/860x394.jpeg?1627511327)



