Connecting state and local government leaders
The Information Technology-Information Sharing and Analysis Center wants to create a coordinated vulnerability disclosure program that could alert vendors about security flaws in their voting systems.
Fueled by monetary rewards and curiosity, hackers have played a significant role in helping companies discover and fix security vulnerabilities in a variety of technology and software applications.
But one year out from the 2020 presidential election, can they do more to help secure voting systems? Technology researchers hope so.
The Information Technology-Information Sharing and Analysis Center (IT-ISAC) is evaluating the feasibility of creating a coordinated vulnerability disclosure (CVD) program that could alert voting system companies about weaknesses.
The first step in establishing a CVD program requires voting vendors to have a system in place for receiving information about discovered vulnerabilities and acting on that information—procedures several vendors have already begun to implement, said Scott Algeier, the executive director of IT-ISAC, a non-profit that serves as a clearinghouse for information on cyber threats to critical infrastructure.
Where the industry can use help is in developing a way to crowd-source vulnerability detection on voting systems.
To address these concerns, IT-ISAC issued a request for information seeking to address challenges unique to rolling out a program across the industry. Since the comment period closed Oct. 21, the group has been reviewing the input provided.
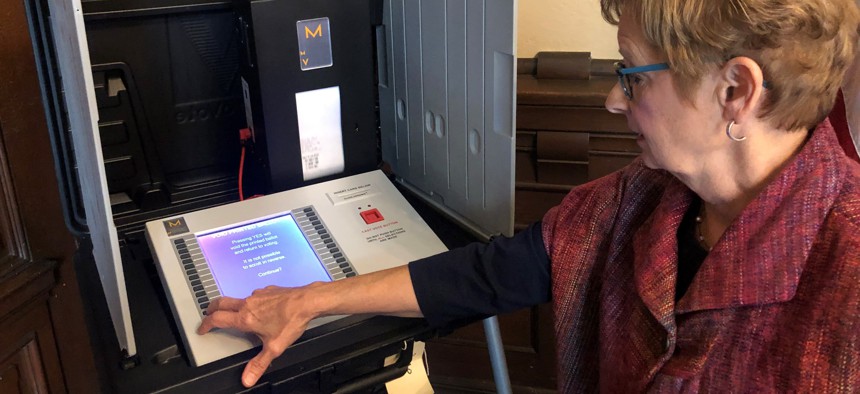
Since U.S. intelligence officials confirmed the extent of Russian interference in the 2016 elections, states and local governments have sought to improve election security, with some transitioning to paper ballots and others purchasing new voting machines. But challenges remain and as foreign adversaries continue to target U.S. elections, “there is a sense of urgency” to shore up voting systems as the 2020 presidential election nears, Algeier said.
Responses IT-ISAC received from its request for information include input on how broad the scope of the CVD program should be, including whether it should incorporate vulnerabilities related to only voting machines or also other election-related infrastructure, Algeier said. There was also a recognition that some modernization will be required on the part of the Election Assistance Commission’s certification processes so that when weak points are found, patches can be deployed and voting systems recertified in a timely manner, he said.
One of the difficulties researchers are trying to address in the request for information is how they can deploy a CVD program centered on elections equipment that is not designed to be connected to the internet. Researchers need physical access to the equipment, so there are security concerns. Because elections systems have been deemed critical infrastructure, Algeier likens it to giving unvetted researchers access to a nuclear power plant.
“You want to make sure the people you are giving access to the voting machines aren’t agents of a foreign power, aren’t people with malicious intent,” he said. “Nobody is suggesting that any random person be able to go inside a nuclear power plant and say ‘I’m a researcher and I want to find out how your code interacts with your nuclear power plant and make sure everything works OK.’”
Despite the difficulties in figuring out a solution, cybersecurity experts say CVD programs should not be optional for voting system vendors given the nature of what is at stake.
“We should not allow our election vendors to put their heads in the sand and pretend vulnerabilities don’t exist,” said Alex Rice, the chief technology officer and co-founder of HackerOne, an online platform that connects companies with hackers who are paid to find the flaws that could let others in.
Companies involved in other aspects of election security have started to roll out disclosure programs to address vulnerabilities. Microsoft recently announced a bug bounty program that could pay up to $15,000 to security researchers who find weaknesses in its ElectionGuard program, which allows voters to verify online that their vote was counted and not altered.
Unlike deploying a software patch through a few lines of code, fixing vulnerabilities discovered on a voting machine can be a time-consuming process that involves physically working on every machine. Algeier said vendors are particularly concerned with ensuring that any problems are communicated in a confidential manner to give them time to fix the issue before information is made public so that vulnerabilities are not exploited.
Such concerns have made headlines during Def Con, an annual hacker conference where participants can test the security of election systems at the conference’s “Voting Village.”
The event has produced scathing reports on security flaws in vendors’ elections systems that have created tension between researchers and the voting system vendors.
The Voting Village event shows there is plenty of interest in the hacker community to address voting system vulnerabilities, Rice said. But without vendor participation, discoveries made at the event may not be helpful.
“There are vulnerabilities that are overblown and there are solutions that are not practical,” Rice said of some of the flaws disclosed through the event. “You need both parties there collaborating to prepare a comprehensive review of what matters and what doesn’t.”
The point of developing a CVD program is to ensure both sides are working together to communicate information about vulnerabilities, Algeier said.
The IT-ISAC is currently reviewing comments it received through the request for information and plans to announce next steps after that review is complete, Algeier said.
Andrea Noble is a staff correspondent with Route Fifty.

NEXT STORY: Automation speeds review of medical records